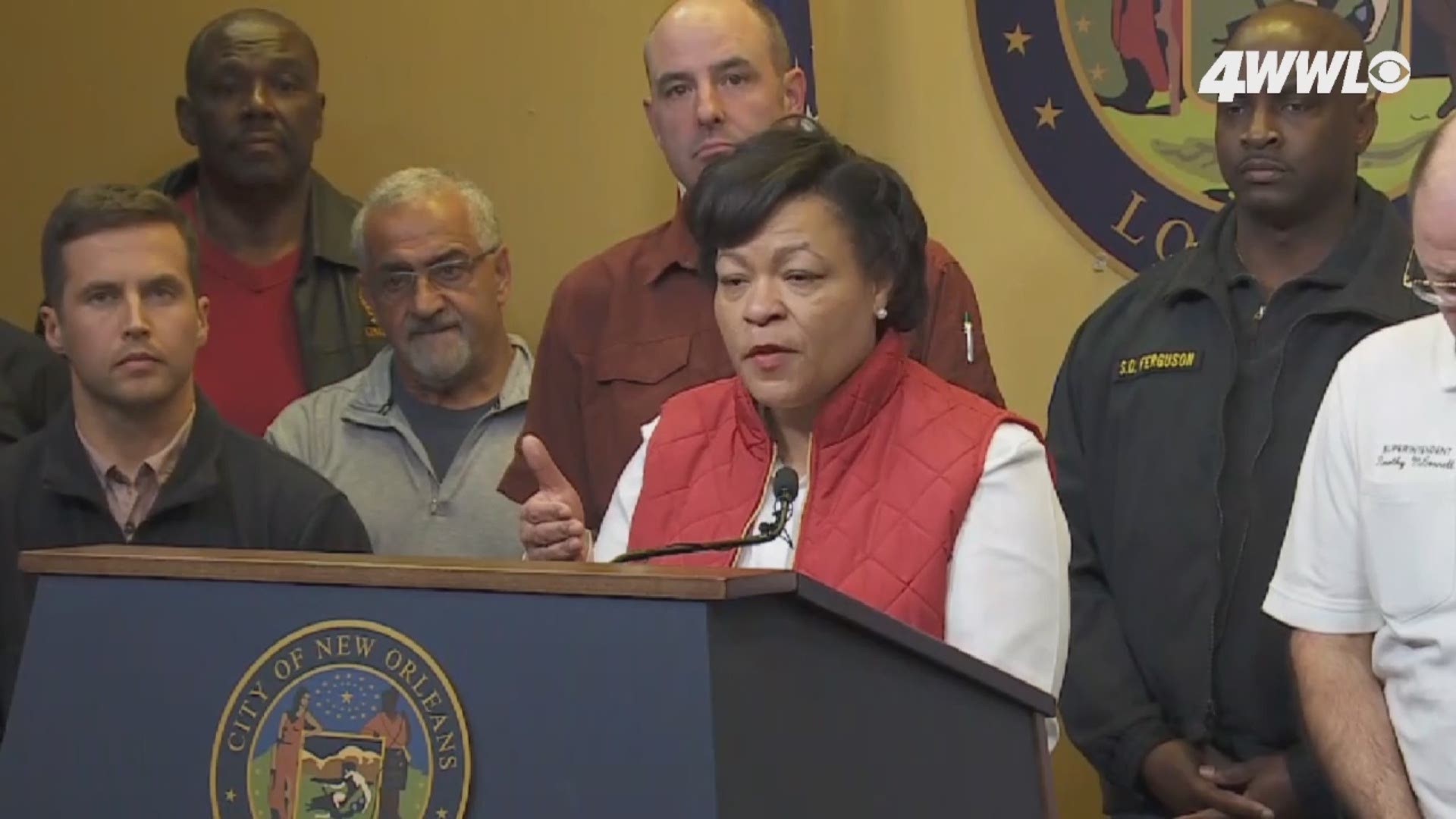
NEW ORLEANS — City officials on Saturday said they are working to restore about 4,000 computers taken offline a day earlier to prevent a cyberattack from spreading.
"We are in recovery mode," New Orleans Mayor LaToya Cantrell said. "It's like you're building a new house."
Rebuilding the house
First, IT crews are "re-imaging" city computers, meaning a fresh installation of the operating systems that let employees use them. After the software is re-installed in city computers, they will be hooked up to backup systems the city maintains.
The backup systems contain the city's files, about 7,000 terabytes of information. Restoring those files is equivalent to painting the walls and bringing furniture into a newly completed house.
Luckily, experts say the ransomware that triggered this process was caught early.
"We expect that data loss has been very minimal," said Kim LaGrue, the city's IT director. She said she could not go into details about how the city protects data because it could tip off hackers. But she said her team has begun to move away from analyzing the breach as it restores computers.
"At this point we have enough information to move into recovery of our systems," she said.
Officials did not say when they expect full service to be restored.
How it happened
LaGrue said authorities have figured out how the hack happened: someone figured out an employee's username and password.
Once attackers were in, they began to encrypt the files on the city's servers.
"Data loss can be equated with encryption," LaGrue said. Once attackers have encrypted the data, it is locked away and inaccessible unless the attackers are paid.
"They want to hold that data ransom or hostage," LaGrue said. City officials said Friday that they had not received any ransom demands, and did not provide an update Saturday on that detail.
But the city keeps backups of information in case a cyberattack happens. That means almost all data can be recovered once the attack is flushed from the city's system.
It's unclear exactly who tried to take the city's data hostage, but state officials dealt with a similar attack weeks ago.
That attack shut down most of the state's Office of Motor Vehicles locations for weeks. Officials aren't sure if the two are related.
"While this one may have some similar characteristics, this one is unique," LaGrue said.
What's still running?
Most city processes have been shut down by the ransomware, because city employees were instructed to turn off and unplug their computers around 11 a.m. Friday, once the hack was detected.
Basic functions such as email remained offline Saturday, but some systems such as 911 and 311 remain operational.
Services affected include:
- All City Hall offices
- NOPD and NOFD computers -- operating through radio only
- EMS computers -- operating through radio only
- Clerk of Criminal Court -- operating with internal database and paper records
Services not impacted:
- 911 -- operates on a separate server
- Civil Court -- operates on a separate server
- Parking enforcement -- tickets are still being issued
311 has the capability to take phone calls for people who need to reach the Department of Safety and Permits.
But there are specific numbers for agencies within the Department of Safety and Permits, while services are offline:
(504) 658-7130 building inspections
(504) 658-7145 electrical
(504) 658-7153 mechanical
(504) 658-7170 school buses and taxis
Meanwhile on the streets ...
Department of Homeland Security Director Collin Arnold told reporters that vandals on Friday night wanted to see if the city's claim that the real-time crime cameras were still working was true.
"Two persons last night decided to test our system by vandalizing six of our cameras with spray paint," Arnold said.
Video from the vandalized cameras was downloaded and sent to the NOPD.
NOPD Chief Shaun Ferguson confirmed that the department was investigating the vandalism.
"We do not take that lightly," he said. "The camera system is very much embedded in the New Orleans Police Department."
You can watch the full Saturday update on the attack here:
More Stories:
► Get breaking news from your neighborhood delivered directly to you by downloading the new FREE WWL-TV News app now in the IOS App Store or Google Play.